May 15, 2026 by sig9
Hacker Wars - May 15, 2026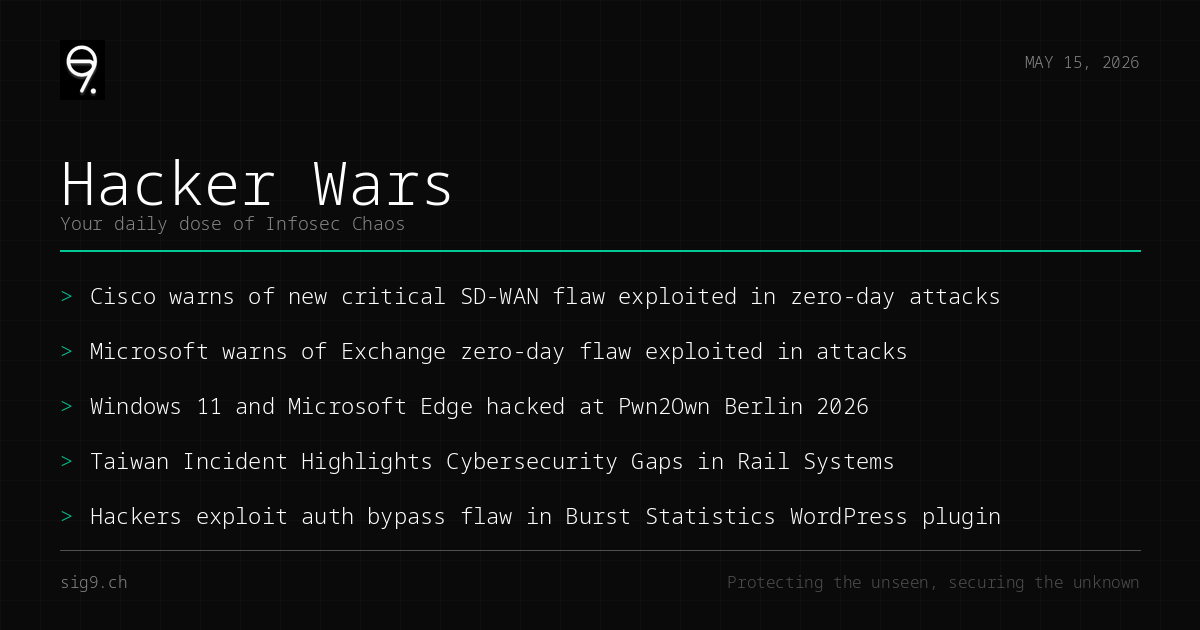
Your daily dose of infosec chaos
Another day, another CVSS 10.0 zero-day actively eaten in the wild - this time Cisco’s SD-WAN gets the honors. Microsoft Exchange also decided to join the party with an XSS zero-day, because apparently Patch Tuesday wasn’t enough excitement this week. Oh, and a student shut down bullet trains with a radio. You know, just a normal Thursday.
Cisco SD-WAN Zero-Day Grants Full Admin Access (CVE-2026-20182)
Cisco confirmed that a maximum-severity authentication bypass in the Catalyst SD-WAN Controller is being exploited in the wild, handing attackers administrative control over affected devices. This is the second CVSS 10.0 flaw in Cisco’s SD-WAN stack exploited this year - which is a pattern, not a coincidence.
What to do: Patch your SD-WAN controllers immediately. If you can’t patch today, restrict management interface access to trusted networks only.
Microsoft Exchange XSS Zero-Day Targets Outlook Web Users
Microsoft published mitigations for a high-severity cross-site scripting flaw in Exchange Server that’s already being weaponized against Outlook on the web users. Attackers can execute arbitrary code in the victim’s browser context - classic stored XSS, but in your mail server.
What to do: Apply Microsoft’s recommended mitigations and monitor Exchange logs for unusual OWAscript.aspx requests.
Pwn2Own Berlin Day One: 24 Zero-Days, Half a Million in Payouts
Security researchers walked away with $523,000 on day one of Pwn2Own Berlin after demonstrating 24 unique zero-days against Windows 11, Microsoft Edge, and other targets. The highlights included full system compromises that would make any red team proud.
What to do: Nothing actionable yet, but expect a flood of patches from Microsoft and friends in the coming weeks. Stay tuned.
Student With Software-Defined Radio Shuts Down Taiwan Bullet Trains
A Taiwanese student experimenting with software-defined radio technology managed to halt three high-speed trains for nearly an hour, triggering an anti-terrorism response. The incident exposed glaring gaps in rail system cybersecurity - specifically, the lack of signal authentication in critical transit infrastructure.
What to do: If you operate ICS or OT environments, assume radio-frequency attacks are within reach of motivated amateurs. Review your physical-layer security.
WordPress Burst Statistics Plugin Has Actively Exploited Auth Bypass
A critical authentication bypass vulnerability in the Burst Statistics WordPress plugin is being exploited to gain admin-level access to websites. If you run WordPress and this plugin sounds familiar, this is your wake-up call.
What to do: Update Burst Statistics immediately. If you’re not using it, audit your WordPress plugins for anything you don’t recognize.
That’s all for now. Patch your stuff and don’t click suspicious links.
Brought to you by sig9 - sig9.ch | Protecting the unseen, securing the unknown
This bulletin is provided for informational purposes. Contact us for tailored security analysis.