May 14, 2026 by sig9
Hacker Wars - May 14, 2026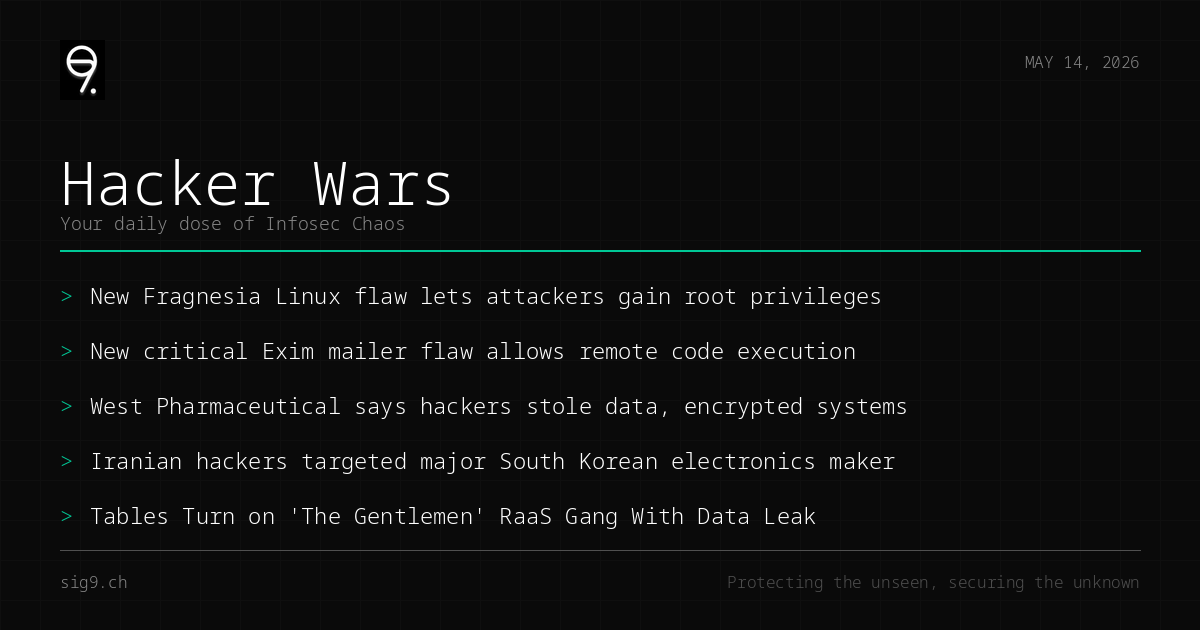
Your daily dose of infosec chaos
Kernel vulns, mail server disasters, and ransomware gangs getting doxxed by their own sloppy OPSEC. Just another Wednesday in infosec.
New Fragnesia Linux Flaw Gives Attackers Root Access
A fresh kernel vulnerability dubbed “Fragnesia” (CVE-2026-46300) lets local attackers escalate to root on affected Linux systems. Distros are already pushing patches, but if you’re running unpatched kernels in production, congratulations - you’re a sitting duck.
What to do: Patch your Linux kernels immediately. Check your distro’s security advisories and prioritize internet-facing hosts.
Critical Exim RCE Flaw Threatens Mail Servers Worldwide
The Exim mail transfer agent has a critical remote code execution bug that doesn’t even require authentication to exploit. If you’re running Exim in certain configurations, an attacker can execute arbitrary code on your mail server without credentials. That’s about as bad as it gets.
What to do: Update Exim to the latest patched version. If you can’t patch right now, consider restricting access to your SMTP ports and reviewing your Exim configuration for affected options.
West Pharmaceutical Confirms Ransomware Attack With Data Theft
West Pharmaceutical Services disclosed a cyberattack where hackers both stole data and encrypted systems - the classic double extortion playbook. The healthcare/pharma sector continues to be a favorite target, because nothing says “pay up” like threatening to leak sensitive data.
What to do: Review your organization’s incident response plan and ensure backups are air-gapped and tested. If you’re in healthcare, assume you’re a target.
MuddyWater Expands Espionage Campaign Across Asia
Iran’s MuddyWater group has been busy - at least nine organizations across multiple countries and sectors got hit in a broad cyber-espionage campaign. A major South Korean electronics manufacturer was among the targets. State-sponsored groups don’t take days off.
What to do: Review network segmentation and monitor for known MuddyWater TTPs, including suspicious use of legitimate remote management tools.
The Gentlemen RaaS Gang Gets a Taste of Their Own Medicine
In a delightful turn of events, an OPSEC failure exposed the internal workings of “The Gentlemen” ransomware-as-a-service operation. The leak reveals their affiliate model, tactics, and organizational structure. Turns out even cybercriminals struggle with operational security sometimes.
What to do: Use the leaked IOCs and TTPs to update your threat detection rules. If you’re tracking ransomware groups, this is a goldmine of intel.
Catch you tomorrow. In the meantime, go check your attack surface.
Brought to you by sig9 - sig9.ch | Protecting the unseen, securing the unknown
This bulletin is provided for informational purposes. Contact us for tailored security analysis.