May 13, 2026 by sig9
Hacker Wars - May 13, 2026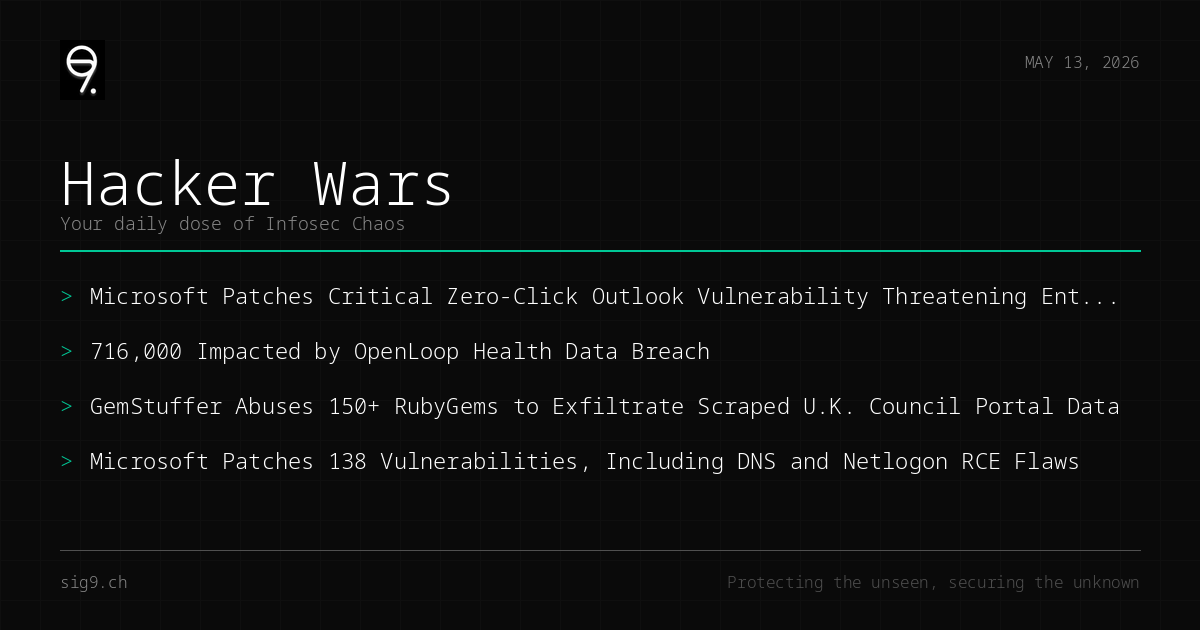
Your daily dose of infosec chaos
Patch Tuesday dropped like a bad habit this week, and Microsoft is serving up zero-click Outlook vulns like it’s 2016 all over again. Meanwhile, healthcare data keeps walking out the door, and someone figured out how to turn RubyGems into a covert exfiltration channel. Grab your coffee and let’s dig in.
Microsoft’s Zero-Click Outlook Flaw Is Back From The Dead
CVE-2026-40361 is a critical zero-click vulnerability in Outlook that echoes the infamous BadWinmail bug from a decade ago - the one they called an “enterprise killer.” This time around, attackers can trigger code execution just by sending you an email. No clicks, no macros, no user interaction required. The vulnerability exists in how Outlook processes certain message formats, and exploitation is about as stealthy as it gets.
What to do: Patch immediately. If you can’t patch yet, disable TNEF parsing in Outlook and monitor for suspicious process spawning from outlook.exe.
OpenLoop Health Breach Exposes 716,000 Patients
Telehealth platform OpenLoop Health got popped back in January, and they’re just now telling the 716,000 affected users that their personal data went on a field trip. The breach exposed names, addresses, dates of birth, and health information - basically the full identity theft starter pack. The company took four months to disclose, which is… not great.
What to do: If you’re an OpenLoop user, freeze your credit and watch for suspicious medical claims. Healthcare orgs: review your third-party vendor security posture yesterday.
GemStuffer Turns RubyGems Into A Data Exfiltration Pipeline
Researchers uncovered a novel campaign called GemStuffer that planted over 150 malicious packages on RubyGems. But here’s the twist - these gems weren’t designed to infect developers. Instead, they used the registry as a covert channel to exfiltrate data scraped from U.K. council portals. It’s supply chain abuse with a creative pivot: instead of poisoning code, they’re abusing the package ecosystem as dead-drop infrastructure.
What to do: Audit your dependencies. Run bundler-audit and review any recently installed gems. Consider pinning gem sources to trusted registries.
Microsoft Drops 138 Patches Including DNS And Netlogon RCE
Patch Tuesday brought 138 vulnerabilities to fix across Microsoft’s product lineup, with 30 rated Critical. The highlights include remote code execution flaws in DNS and Netlogon - the kind of bugs that let an unauthenticated attacker own your domain controller from across the network. None are known to be exploited in the wild yet, but give it about 48 hours.
What to do: Prioritize the DNS and Netlogon patches on domain controllers. Test and deploy the Outlook fix ASAP. Everything else can follow your normal patch cycle.
That’s the chaos for today. Stay sharp out there.
Brought to you by sig9 - sig9.ch | Protecting the unseen, securing the unknown
This bulletin is provided for informational purposes. Contact us for tailored security analysis.