May 11, 2026 by sig9
Hacker Wars - May 11, 2026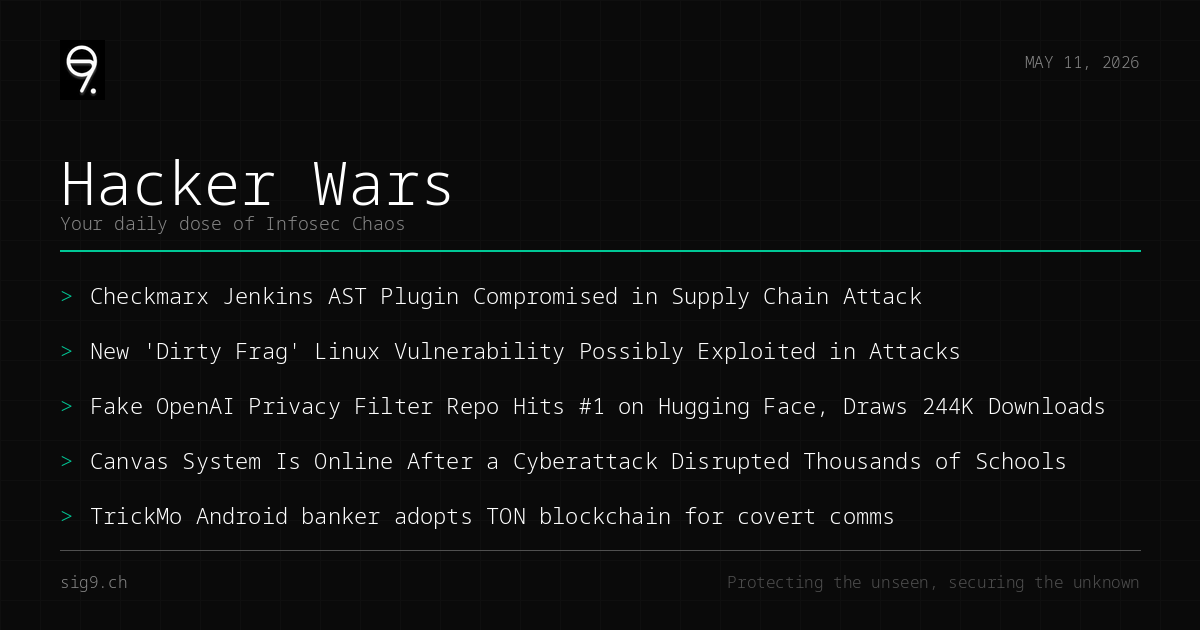
Your daily dose of infosec chaos
Today we’ve got supply chain attacks hitting security tools, a Linux vuln with a familiar dirty name, and malware getting creative with blockchain. Again, if you thought AI repos were safe, think again. Grab your coffee and let’s dive in.
Checkmarx Jenkins Plugin Gets Backdoored in Supply Chain Attack
A malicious version of the Checkmarx Jenkins AST plugin was pushed to the Jenkins Marketplace last week. If you’re running this in your CI/CD pipeline, you might have invited an attacker to the party.
What to do: Audit your Jenkins plugins immediately and verify checksums against the official Checkmarx releases.
Dirty Frag: New Linux Vulnerability Under Active Exploitation
CVE-2026-43284 and CVE-2026-43500, collectively known as “Dirty Frag” (or Copy Fail 2), have been disclosed before patches were ready. The vulnerability affects Linux systems and is possibly already being exploited in the wild.
What to do: Monitor for kernel patches from your distro and consider disabling affected features until a fix is available.
Fake OpenAI Repo Hits #1 on Hugging Face With 244K Downloads
A malicious repository impersonating OpenAI’s Privacy Filter model climbed to the top of Hugging Face’s trending list. The Rust-based stealer hit Windows users who trusted the repo without verifying its authenticity. Supply chain attacks in the ML ecosystem are becoming a real problem.
What to do: Always verify model publishers and check repository metadata before downloading from Hugging Face.
Canvas LMS Back Online After Cyberattack Disrupted Schools Worldwide
The Canvas learning management system is back online after a cyberattack knocked it offline during exam season. Tens of thousands of students were affected globally. Details on the attack vector are still sparse, but the timing suggests deliberate targeting.
What to do: If your organization uses Canvas, review access logs and ensure MFA is enabled for all accounts.
TrickMo Malware Adopts TON Blockchain for Stealthy C2 Communications
The TrickMo Android banking trojan is now using The Open Network (TON) blockchain for command-and-control communications. This makes takedowns significantly harder since blockchain infrastructure is decentralized and resilient. European users are the primary targets.
What to do: Keep your Android devices updated and avoid sideloading apps from unofficial sources.
Catch you tomorrow. In the meantime, go check your attack surface.
Brought to you by sig9 - sig9.ch | Protecting the unseen, securing the unknown
This bulletin is provided for informational purposes. Contact us for tailored security analysis.