May 8, 2026 by sig9
Hacker Wars - May 08, 2026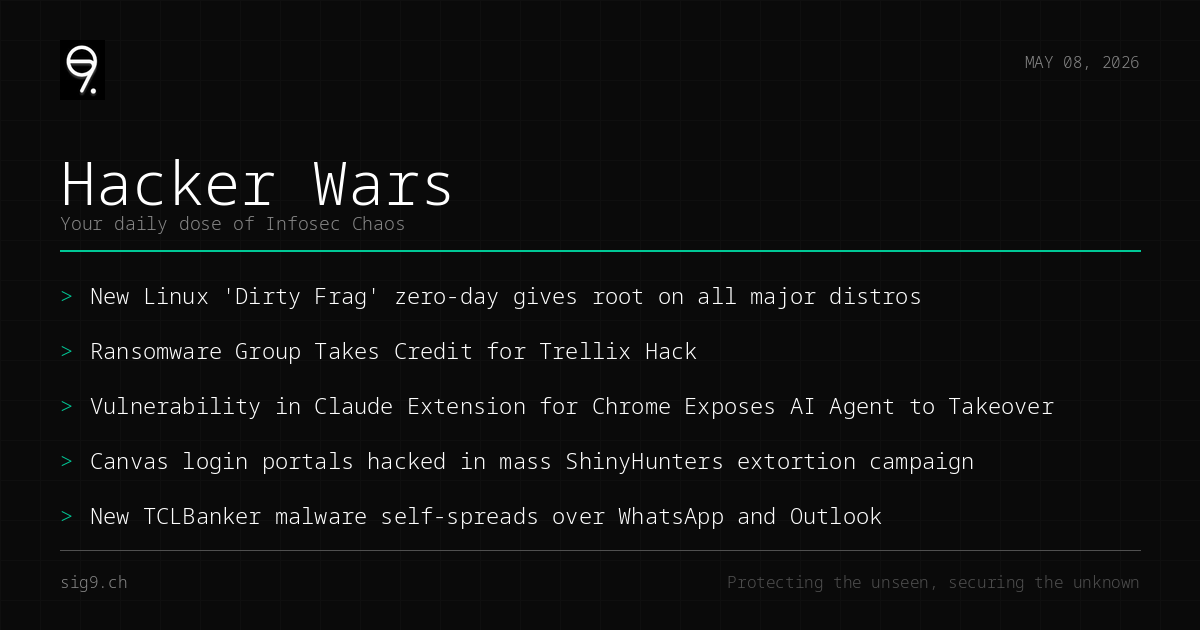
Your daily dose of infosec chaos
Today’s theme: everything is on fire, and some of it is your fault. We’ve got a Linux kernel zero-day with a PoC already in the wild, a security vendor getting pwned by the very threat actors they’re supposed to stop, and AI agents getting hijacked through sloppy Chrome extensions. Buckle up.
Dirty Frag: Linux Kernel Zero-Day Hands Attackers Root Everywhere
A new local privilege escalation vulnerability dubbed Dirty Frag - a spiritual successor to the infamous Dirty Pipe - lets any local user escalate to root on most major Linux distros with a single command. The PoC is already public, and patches are still pending for many distributions.
What to do: Monitor your distro’s security advisories religiously, restrict local access to critical systems, and consider disabling unprivileged user namespaces until patches land.
RansomHouse Pwns Trellix, Security Industry Pretends Not to See
RansomHouse - a ransomware group - has breached Trellix, the security vendor formed from the merger of McAfee Enterprise and FireEye. They’ve posted screenshots of internal access as proof. The irony of a security company getting hit by the exact threats they sell protection against is almost too perfect.
What to do: Review your own vendor risk management. If your security vendor can’t secure themselves, what does that say about your supply chain?
Claude Chrome Extension Vulnerable to Prompt Injection Takeover
Researchers found that Anthropic’s Claude browser extension for Chrome has weak permission boundaries and flawed trust logic, allowing malicious web pages to inject prompts and hijack the AI agent. Your helpful AI assistant could be silently turned against you while you browse.
What to do: Disable or remove the Claude Chrome extension until a patched version is released. If you must use it, avoid browsing untrusted sites with the extension active.
ShinyHunters Defaces Hundreds of Canvas Login Portals
The ShinyHunters extortion gang hit Instructure’s Canvas LPS again, this time defacing login pages for hundreds of universities and school districts with ransom demands. Students and faculty were met with threats to leak stolen data instead of their usual login screens. Education remains a soft target.
What to do: If your organization uses Canvas, monitor for official breach notifications, force password resets for affected accounts, and brief users on phishing risks stemming from potential data exposure.
TCLBanker Spreads Itself Through WhatsApp and Outlook
A new banking trojan called TCLBanker is spreading via trojanized Logitech AI Prompt Builder installers, then self-propagating through WhatsApp and Outlook messages. It targets 59 banking, fintech, and crypto platforms. The malware is borrowing worm-like tactics from the 2010s playbook, and apparently it still works.
What to do: Don’t download software from unofficial sources. Alert your SOC to watch for unusual MSI installer activity and outbound connections to banking domains from non-finance endpoints.
Catch you tomorrow. In the meantime, go check your attack surface.
Brought to you by sig9 - sig9.ch | Protecting the unseen, securing the unknown
This bulletin is provided for informational purposes. Contact us for tailored security analysis.